Endpoint Detection & Response
Features
Ensure security and information safety for any computer network, provide features to detect and prevent risks, including the main components:
+ Advanced EDR: Allows data collection, investigation and rapid response to risks;
+ Dynamic Deception: Detect intrusion dynamically & effectively;
+ Internal risk prevention: Detect behaviors that violate the security policies such as: using USB or mobile devices to copy data; Accessing websites that are not allowed; Upload or perform actions that may cause data leakage;…
SPECIFICATIONS
Features
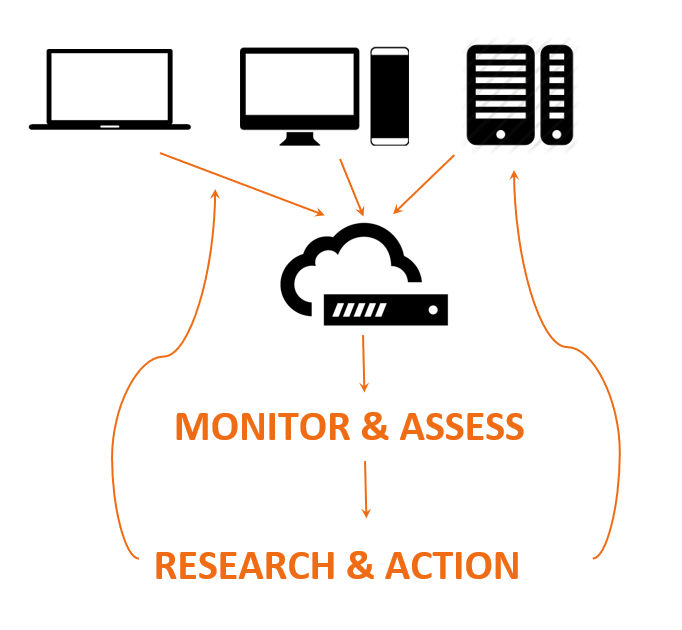
+ A very lightweight (<1% CPU) software sensor deep in kernel is installed on each computer and device (i.e. endpoint) in an organization to monitor all data and activities
+ Activity is collected and analyzed on an internal server or in the cloud using Veramine pipelines of algorithms, combining rule-based and machine learning approaches
+ Security analysts totally control the system, monitor all activities, collect forensics artifacts and are alerted to suspicious activity and can assess further. Minimizing false positives is essential
+ Once activity is assessed as malicious, analysts can take action to investigate and remediate
+ Prevention rules can be updated automatically or manually
+ Deception traps are deployed to designated places to trick attackers